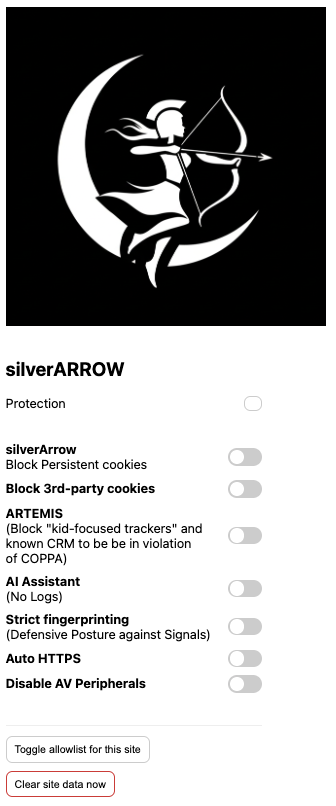
PROJECT silverARROW
SilverArrow v1.1.0-beta.1
Java Application to Block Trackers and Persistent Cookies
"Safeguarding the vulnerable"
Project silverARROW is an application, inspired by the Greek goddess Artemis, that reduces the attack surface and guards the Confidentiality, Integrity, and Availability of users data from invasive Cookies and CRM's.
In Greek Mythology, the goddess, Artemis, symbolizes "defense, stealth, and safeguarding the vulnerable." Her signature weapon is the bow and arrows. They symbolize her prowess as the goddess of the hunt and her role as a protector of the wild and the vulnerable.
Project Notes:
1. Integrate Components -Initialize CookieManager with BlacklistCookiePolicy at app startup. -Register CookieBlockerFilter in your servlet container (e.g., Tomcat).
2. Combat Evercookie-Style Persistence -Prevent cookie resurrection: Clear all storage mechanisms (LSO, IndexedDB) via JavaScript injection (requires embedded browser engine like JCEF). -Block storage APIs using a Proxy to intercept localStorage/sessionStorage calls.
3. Limitations and Considerations -Browser-Level Restrictions: Java apps can’t directly modify browser storage; use embedded browsers (JCEF) for full control. -CRM Tracking Evasion: Block known CRM endpoints via DNS filtering (e.g., integrate with dnsjava). -Performance: Cookie inspection adds ~5-10ms latency per request (optimize with caching).
4. Define Blocking Rules Maintain a configuration file (e.g., blocklist.properties) with: